Last updated: April 4th, 2023 at 13:26 UTC+02:00
SamMobile has affiliate and sponsored partnerships, we may earn a commission.
Reading time: 3 minutes

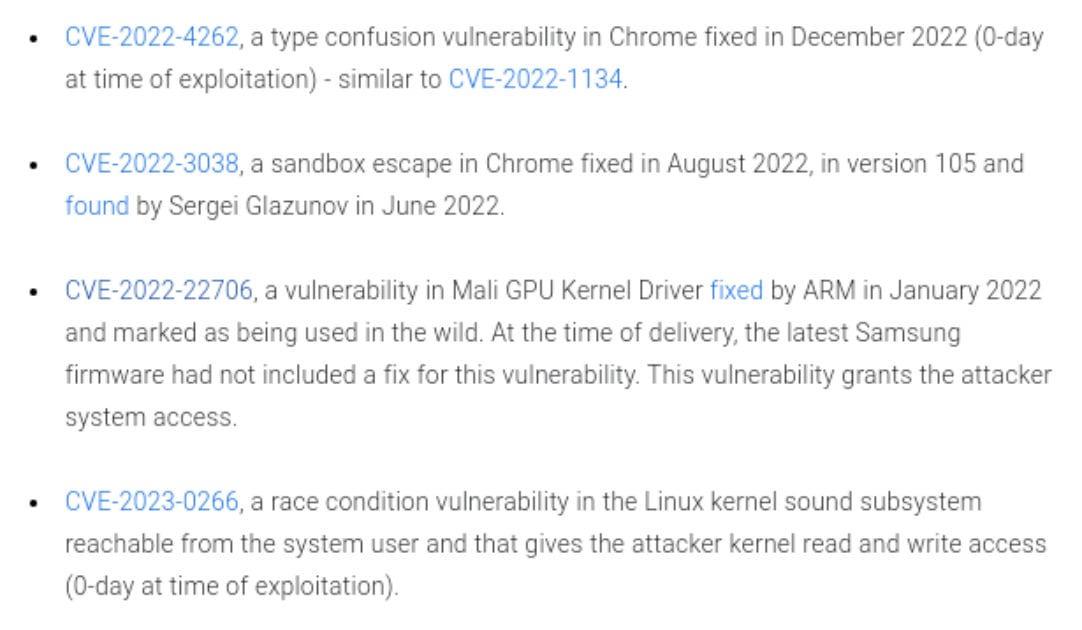
Google's Threat Analysis Group (TAG) revealed the exploit chain earlier today. In December 2022, TAG discovered this exploit chain that relies on multiple 0-day and n-day vulnerabilities and targets the Chrome and Samsung Internet browsers.
More specifically, two vulnerabilities in this chain concern Chrome. And since Samsung Internet Browser uses Chromium, the app was used as an attack vector in conjunction with the Mali GPU kernel driver vulnerability reported last year. This Mali exploit grants attackers system access.
Through this chain of exploits, hackers would send one-time links via SMS to Samsung Galaxy devices located in the UAE (United Arab Emirates). The links would redirect unsuspecting users to a page that would deliver “a fully featured Android spyware suite written in C++ that includes libraries for decrypting and capturing data from various chat and browser applications.”
What's the current situation? Well, Google fixed those two Chrome vulnerabilities mentioned above and patched its own Pixel phones at the beginning of 2023. Samsung also fixed its Samsung Internet browser in December 2022. The Korean tech giant addressed the two flaws related to Chromium (CVE-2022-4262 and CVE-2022-3038) through an Internet browser app update after version 19.0.6.
Samsung broke the exploit chain that was leveraging its Chromium-based Internet app and the Mali kernel vulnerability in December, and it appears that the attacks on users in the UAE have stopped. However, one glaring issue remains.
The exploit chain Google detailed today was addressed thanks to Samsung Internet browser updates in December. But one link in the chain, consisting of the massive Mali security vulnerability (CVE-2022-22706), remains unpatched on Samsung devices equipped with Exynos chipsets and Mali GPUs. That is, despite the fact that Mali already provided a fix for its kernel driver exploit as early as January 2022.
Until Samsung mends this issue through a security firmware patch containing the Mali fix, it appears that the majority of Galaxy devices featuring Exynos SoCs remain vulnerable to the Mali GPU kernel driver exploit.
Update: Samsung reached out to us with the following statement “Samsung takes the security of its products very seriously. We have already taken necessary steps to prevent these potential exploit chains by issuing patches for the Samsung Internet app in December 2022. December's updates to the Samsung Internet app disable entry points for the remaining vulnerabilities and ensure devices are protected.
We are actively collaborating with our partners to release patches for the remaining vulnerabilities as early as possible, starting April, and recommend all users keep their devices updated with the latest software to ensure the highest level of protection possible.”
Mihai is a blogger and column writer at SamMobile. His first Samsung phone was an A800 which took a lot of beating, and a part of him still misses the novelty of the clamshell design. In his free time, he enjoys watching shows, documentaries, and stand-up comedy; listening to music, taking walks, and occasionally playing old(er) video games.