Last updated: December 23rd, 2022 at 12:46 UTC+01:00
SamMobile has affiliate and sponsored partnerships, we may earn a commission.
Reading time: 2 minutes

Experts at Group-IB, ThreatFabric, and Cyble have found a new Android banking malware called “Godfather” that has targeted users in 16 countries. The banking malware is speculated to be the successor of Anubis, which itself was once a very widely-used banking trojan by hackers.
According to reports, the Godfather Android banking malware has been targeting users in 16 countries by stealing their account credentials for over 400 online banking sites and cryptocurrency exchanges. It can mask itself as the login screen on top of the banking and cryptocurrency exchange websites' app login forums. When the user inputs his/her credentials, the information isn't submitted to the official website but is submitted to the hackers.
ThreatFabric spotted the Godfather banking malware in 2021, but according to the latest report by Cyble, the malware has undergone massive code changes and can now bypass the latest Android security measures. When the malware detects the affected endpoint and determines that the app language is Russian, Azerbaijani, Armenian, Belarusian, Kazakh, Kyrgyz, Moldovan, Uzbek, or Tajik, it shuts down. This is because the developers of this malware are believed to be of Russian origin.
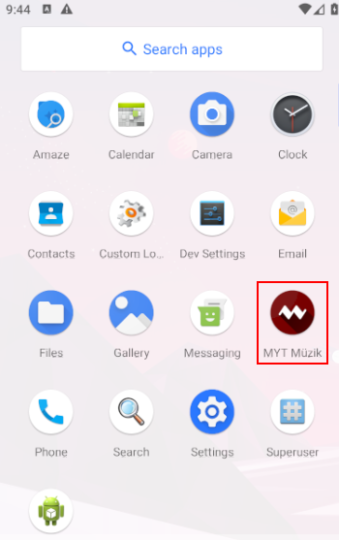
The actual numbers of the infected devices aren't known yet, because infection via the Play Store is not the only way this malware has stolen banking and crypto exchange information from users. However, thanks to Cyble, one of the infected apps masks itself as MYT Müzik and has over 10 million downloads. Once downloaded, the app asks for permissions such as Google Protect and Accessibility Services.
After the permissions are granted, the app takes over the victim's SMS and notifications and starts recording the screen. It also extracts contacts, call lists, and more. The Godfather Android malware has targeted 215 banking apps, and most of them are located in the USA (49), Turkey (31), Spain (30), Canada (22), France (20), Germany (19), and the UK (17). Other targets of the Godfather malware include 110 cryptocurrency exchange platforms and 94 cryptocurrency wallet apps.